Update on 23 July 2024: This article has been updated to include new details about the massive scale of the MediSecure breach and what we currently know about the stolen data.
When Australia’s national cybersecurity coordinator announced that a large-scale ransomware data breach was impacting a commercial healthcare organisation, it would be a while longer before media reports began indicating that the organisation was e-prescriptions provider MediSecure.
Since then, MediSecure has confirmed the attack and revealed that over 12.9 million customers were impacted, making it one of the largest data breaches in Australia's history. Here's everything we know about the cyberattack and what's happened to the data.
Who is MediSecure?
MediSecure was one of Australia's two major e-scripts providers, facilitating electronic prescribing and dispensing across the nation. Given the organisation's size, it's not surprising that it held a massive trove of data.
In May 2024, MediSecure confirmed that it had identified a cybersecurity incident that put private personal and health information at risk. At the time, the scale of the attack was not publicly known, and both Australia's national cybersecurity coordinator and a MediSecure spokesperson stated that investigations were underway.
How did the MediSecure ransomware attack happen?
In a statement on the MediSecure website, the business says the incident likely stemmed from a third-party vendor and that it had taken immediate mitigating steps.
“While we continue to gather more information, early indicators suggest the incident originated from one of our third-party vendors. MediSecure takes its legal and ethical obligations seriously and appreciate this information will be of concern.”
Third-party vendors are a common attack vector for cybercriminals. In our discussion with Lance Rubin, founder/owner of financial modelling consultancy Model Citizn, Lance explained that his business was targeted because they worked closely with large organisations and government entities.
“It’s not you as a business, it’s actually how you're connected to the broader, industry finance ecosystem... I'd say that probably anyone who's in financial services and a small business is probably at a greater risk because we're so trusted, because we've got access to our clients information. And therefore it's not necessarily our own data [that hackers want], it's our client’s data.”
What is a ransomware attack, exactly?
Australia has seen a growing number of high-profile ransomware attacks, including those against Medibank, Latitude Financial and HWL Ebsworth.
Ransomware attacks involve a malicious actor infiltrating a system to lock or encrypt your files, assets and data, then demanding a ransom for the release of those files. A now-ubiquitous tactic involves demanding a ransom not to leak or sell highly sensitive information or intellectual property. For organisations that store data relating to legal, financial or health-related areas, the dissemination of that information can be especially devastating – unfortunately, this makes them a common target for ransomware attacks.
In particular, healthcare organisations are popular targets for cyberattacks. A similar attack rocked the entire US health system, when a cyberattack immobilised one of the country's largest health payment and prescription processors, Change Healthcare. The attack resulted in critical delays impacting pharmacies, clinics, hospitals and insurers.
What happened in the wake of the MediSecure cyberattack?
MediSecure immediately stated it was cooperating with the Australian Digital Health Agency and national cybersecurity authorities to manage the incident's impacts. Previously, it held a government contract for providing PBS e-script services until late 2022, when exclusivity was granted to another firm, eRx.
The Australian Medical Association president pushed for urgent briefings, calling for a thorough, transparent investigation backed by clear public communication to maintain trust in electronic health systems.
In June 2024, MediSecure went into voluntary administration after it failed to secure a financial bailout from the government. By July, the organisation revealed that the incident had impacted nearly 13 million customers.
What has happened to the stolen data of 12.9 million Australians?
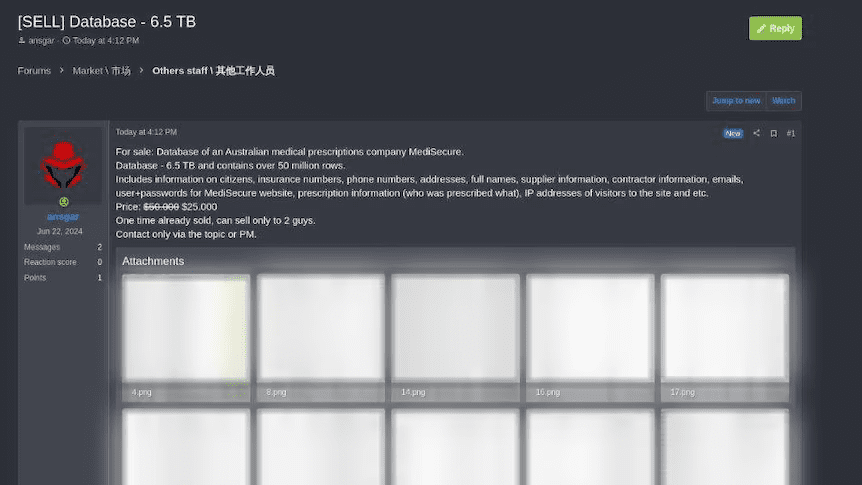
Given the nature of the dark web, it's notoriously difficult to confirm what happens to stolen data. But there's reason to believe that the MediSecure data is already in the hands of a threat actor.
In reporting by the ABC, cybersecurity analysts say the data was almost certainly already sold on the dark web for $50,000 (likely USD). That same ABC reporting further reveals that a post on a separate forum is again spruiking the data, this time at half price.
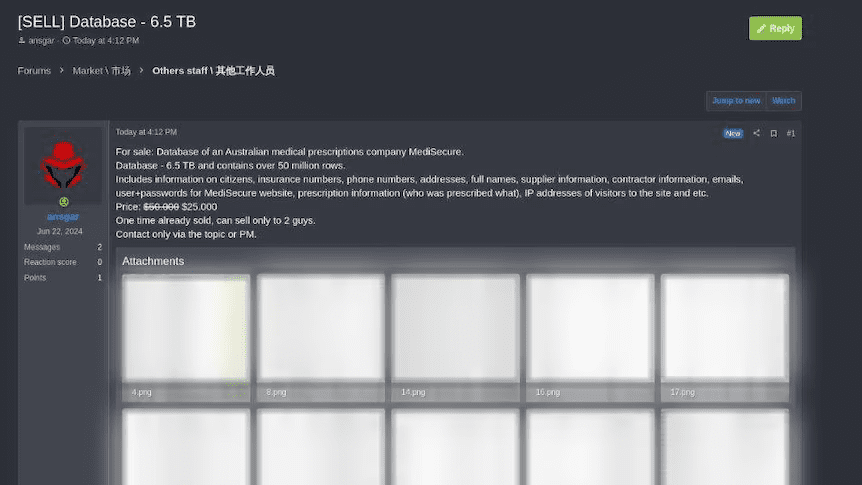 Source: ABC
Source: ABC
Stolen data can heighten your AP team’s cyber risks
Ransomware attacks have devastating consequences for the organisations and individuals impacted, but there are knock-on effects even for those who aren’t directly affected. A joint police operation claims to have linked 11,000 cybercrime incidents to the Medibank data breach, illustrating how stolen data can act as kindling for other cyberattacks.
Many accounts payable (AP) and finance professionals are on the frontlines of business scams and cybercrime. With stolen data facilitating even more scams, consider two important areas necessary for protecting yourself:
Employee awareness. Staff need to be kept informed and alert to the potential for scams and the warning signs to notice. This means regular training but also keeping them up-to-date on the latest breaches, risks and scam tactics.
Anti-fraud processes. Humans are fallible, which means that employee awareness cannot and should not be your final line of defence. Instead, look for automated and centralised ways to enforce strong anti-fraud controls like segregation of duties.
Check to see if your data has been in a breach
If your data has been compromised, you might be a bigger target for scammers. Use our free checker tool to see if your details have been part of any breaches.

 Source: ABC
Source: ABC