Just one click… is all it takes to let a cybercriminal into your digital network.
Email attacks are increasing each year. This means if your accounts payable (AP) staff are not equipped with the knowledge to defend against BEC attacks, your AP staff may be deceived by cybercriminals.
In fact, in the first half of 2022, the ACCC received 11,395 incident reports of business email compromise scams and in total, this cost Australian businesses $57 million.
In week 3 of October’s Cybersecurity Awareness Month, we explore the email security best practices to ensure your finance team's email is secure from spam and phishing attacks.
Email Security Best Practices
Implementing email privacy and security starts when you first create an email account for newly onboarded accounts payable staff. The following email security best practices can be integrated into any organisation:
1. Strong Passphrases
Using several complex passwords across multiple devices is a no-brainer in email security. Yet email accounts are still becoming vulnerable to the use of poor passwords, for example, 66% of Australians responded they use the same passwords for multiple accounts.
Here are some best practices when creating a strong password:
Must be at least 14 characters long
Contains upper and lower-case letters, numbers & special characters
It involves a mix of random letters and words
Unique complex password for every account
If you cannot remember every unique password for all your devices, try using a password manager that could give you peace of mind. We explore using a password manager below.
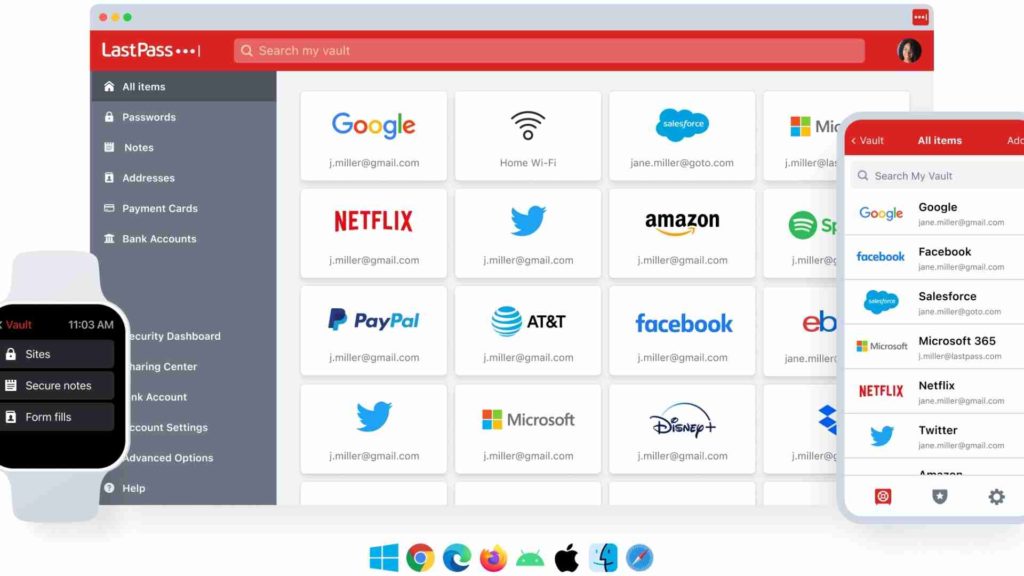
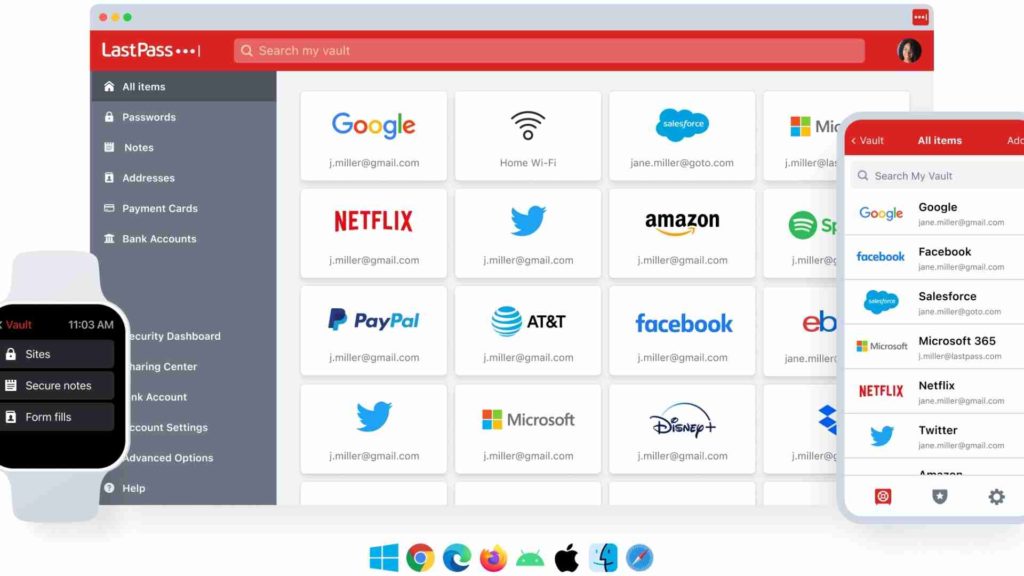
2. Password Manager
Password managers are great for enhancing email security, they allow you to store, generate, and retrieve complex passwords for a variety of applications. This includes email, social media, and other online services.
In addition, password managers can help you generate random strong passwords for each of your applications. When accessing a password manager, employees will only need to remember the master password to access and use the email security tool.
You can start using a password manager like LastPass to stay in control of your cybersecurity and manage multiple passwords at once.
3. Multi-Factor Authentication
Turning on multi-factor authentication (MFA) protects your work emailing accounts with extra login steps. Implementing MFA can provide you with an extra layer of security that can effectively protect against unauthorized access from cybercriminals.
Typically, MFA requires a combination of information from the user when logging into an account. For example:
Something you know (such as a password or PIN code)
Something you have (such as a one-time password, physical token, or smartcard)
Something you are (such as your fingerprint or face scan)
Having two or more authentication factors increases your email security and makes it difficult for cybercriminals to gain access to your account especially if they know the password. To get started with MFA you can do the following:
Download an authenticator app (e.g. Outlook authenticator)
Enable biometrics or fingerprint scanning on your mobile device
Pair your device using SMS, email, or phone call
4. Encrypting Email Messages
Another email security solution to protect sensitive information is encrypting email messages by enabling S/MIME (secure/multipurpose internet mail extensions) on Outlook or Gmail.
By integrating S/MIME your email messages are protected in the following:
How this works is when a user sends an email, the sender encrypts the email using a public key while the recipient decrypts the email using a private key. S/MIME encryption and digital signatures ensure that the email is authenticated, and its content is not manipulated in any way.
Through email encryption, you can establish integrity, uphold privacy, and preserve sensitive data when sending emails.
5. Secure Email Gateway
Secure email gateway providers are a great email security solution if you are looking to block email-based threats like spam, viruses, malware, or denial of service attacks before they reach your mail server.
These unwanted malicious emails can be quarantined, ignored, deleted, or simply bounced back with an error message. When selecting a secure email gateway provider, you should look out for the following features and capabilities:
Scanning capabilities: ability to scan emails and identify threats
Defending against multiple threats: protect against phishing attacks, malware, or malicious email attachments
Advanced security threat identification: AI technology that can evolve in identifying sophisticated attacks
Deployment opportunities: be able to be deployed on any organisational network structure

6. Cybersecurity Awareness Training
Utilising detection and protection security solutions is not enough to prevent cyberattacks.
Cybersecurity awareness training is necessary for organisations in every industry to protect themselves against the rise of cybercrime and sophisticated phishing attacks. The training program should use a variety of tools that will not only engage your employees but also be an ongoing pursuit that allows skills to develop consistently over time.
The best approach to cybersecurity awareness training is involving a blend of formal, computer-based training assignments, and phishing simulations on a monthly and quarterly basis. Some of the topics that need to be addressed in training are:
By prioritising cybersecurity awareness training, you can increase the awareness of email-based threats and significantly reduce the security risk of phishing emails that may lead to data breaches.
How Eftsure Can Help
The best defence against email threats and BEC attacks is implementing cybersecurity awareness training and promoting a cybersecurity culture in the workplace.
Financial leaders and IT teams must collaborate to ensure employees are competent in email security and understand how to handle emails that may seem malicious.
With Eftsure, our fraud tech platform protects your organisation by verifying the banking details you use to process electronic payments. Through payment investigation, you can ensure that the BSB, and account number are correct before releasing funds. This process makes sure that the funds are being sent to the legitimate recipient.
Contact Eftsure today to learn more about staying protected from malicious emails.