Cyber Brief for CFOs: July 2024
All the news, tactics and scams for finance leaders to know about in July 2024.
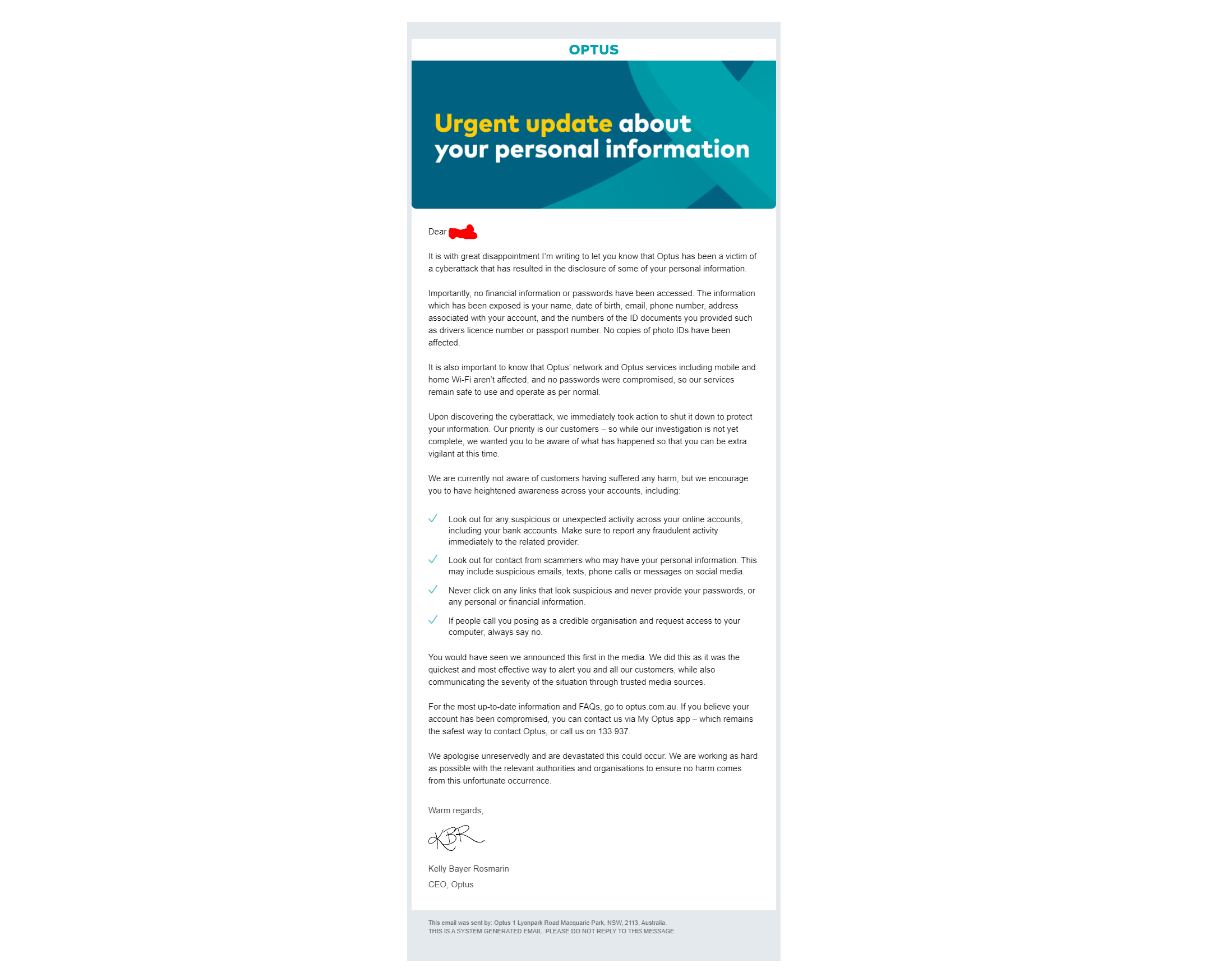
“Optus’ nearly 11 million customers should be ‘extra vigilant’ over the coming weeks for incoming calls, text, and emails as well regularly check with their banks.” That was the paragraph the AFR opened with when reporting on what is possibly the largest data breach in Australia’s history.
While Optus is still investigating the attack with the Australian Federal Police and has claimed it has shut down the attack, AFR’s statement is heavily understating the severity of the breach. Not to mention, the Australian government slamming Optus for the cyber security incident.
CEO, Kelly Bayer Rosin, said in a public statement to the press that it is still unclear who is behind the breach and what their motives are. But, if the cyber attack was conducted with the goal of financial gain, the data will spread quickly over the dark web. Given the sensitivity of the data, many criminals will be interested in acquiring a copy of this database.
It’s been rumoured that some of Optus’ customer data was available for purchase on the Dark Web four days before identifying the Optus data breach.
They will use the data to improve their own fraudulent activities, and just like regular businesses, cyber-criminals who have purchased this data will want to make a profit from it.
The coming weeks and months are likely to see a major spike in phishing emails. Some of these may be sent using the stolen identification numbers, and personal details of individuals. Other phishing emails may claim to be legitimate updates from Optus. And although Optus claims no corporate information was at risk. It will only take one click from someone in your organisation, for cyber-criminals to get access to their devices and emails. So, everyone in your organisation must be extra vigilant of potential scam emails, either to their personal or business email.
The anonymous online account claiming to be behind the data breach has issued an apology for the hack on September 27th. Hours earlier several cybersecurity experts flagged a post by the same account that over 10,000 were published publicly and the poster intended to release another 10,000 records every day. It was the same account that claimed to have the records for sales 4 days prior the data breach.
In their most recent post, the poster has claimed that no ransom was required and the data would be deleted. Whether that will happen will remain a mystery. Optus
As more details have emerged about the hack, experts disagree with Optus’ previous statement that they fell victim to a ‘sophisticated’ hacker. The Open API that was used to acquire the data could have been found by anyone. Several experts claimed that the hack could have been conducted by a teenager and that due to the press coverage they have aborted their ransom requests.

CFOs and specifically Accounts Payable staff must have an even higher degree of caution. While every organisation has at least 1 person that will click on any link in an email, so will the organisations you trade with.
Traditionally, Accounts Payable Managers have been targeted by so-called “push payment redirection scams”. Fraudsters will use a legitimate email address from one of your suppliers. They’ll hijack communication between you and that supplier, intercept an invoice, change the payment details, and redirect payments to their own bank accounts. Once the money is transferred, it’s difficult to recover the funds, and banks disclaim liability for these types of scams. It’s up to Accountants to have the right controls in place to prevent these types of scams.
Accounts Payable needs to be extra vigilant during the vulnerable moments when dealing with supplier payments; when receiving bank account change requests or paying new suppliers for the first time. One of the most effective controls are “supplier call-back controls”. Accounts Payable Managers cannot trust the information they receive in emails and must conduct call-back controls properly.
Optus’ data breach will impact the security of payments and has significantly increased the risk of identity theft. We have written an article about the essential steps to take when you’ve become a victim of Identity theft:
If you have additional questions or are concerned about the implications this data breach may have on your business, feel free to reach out to us or subscribe to the blog, where are publishing many articles around the topic of cybercrime and its implications for CFOs and accountants. For more information contact Optus customer support directly on 133 937, or visit Services Australia webpage that discusses about the current data breach.
All the news, tactics and scams for finance leaders to know about in July 2024.
What is the Fraud and Corruption Policy and how can you ensure your organisation is compliant?
All the news, tactics and scams for finance leaders to know about in April 2024.
Eftsure provides continuous control monitoring to protect your eft payments. Our multi-factor verification approach protects your organisation from financial loss due to cybercrime, fraud and error.