Crowdstrike outage sparks scam surge: how to protect your business
Crowdstrike outage aftermath: Government warnings, scam attempts, and essential steps to safeguard your business from cybercriminals.
You might’ve heard about social engineering, a common cyber-crime tactic. As the gatekeepers of an organisation’s finances, AP teams are often the targets of socially engineered attacks.
So how do they work, how common are they, and what can you do about them?
“Social engineering” describes a range of tactics for getting people to take actions they wouldn’t normally take or revealing sensitive information they wouldn’t normally reveal. While some cyber-crime depends on sophisticated hacking and system infilitration, social engineering typically looks a lot more like old-fashioned deception and manipulation – but, of course, cyber-criminals are liable to pair those tactics with hacked information or infiltration whenever possible.
Basically, social engineering attacks rely on people’s instinct and desire to be helpful to others. It’s a form of psychological manipulation that can happen digitally or in person, but hybrid workplaces and the proliferation of cyber-crime have heightened the risk of digital variants of socially engineered attacks.
For example, a cyber-criminal might impersonate a member of an organisation’s IT team and persuade an AP officer to reveal sensitive payment information. Or they may infiltrate a senior executive’s email and use it to instruct an employee to make a fraudulent payment, often relying on additional tactics like urgency or catching the employee during especially hectic periods.
See detailed examples of social engineering attacks.
This type of social engineering tactic uses a false promise – or ‘bait’ – to lure a victim into doing something that reveals information or helps the scammer infect a system with malicious software (“malware”). For instance, the fraudster might trick an employee into downloading malware by including an email attachment with a title like “Changes to our annual bonus policy.” Who wouldn’t want to know about policy changes that might affect their bank account?
Physical baiting is less common but still exists. This involves leaving equally enticing-sounding flash drives or hard drives in conspicuous places, with the aim of getting employees to connect their devices to them.
Instead of baiting victims with something enticing, scareware relies on motivating them with something, well, scary. This can include false warnings that the target’s device has already been infected or compromised in some way. The goal is to persuade users into downloading a ‘solution’ that actually exposes them to malware or data theft.
Pretexting uses stories or impersonation to gradually get targets to reveal useful information – including highly sensitive information like banking details or personally identifiable information about themselves or others.
The scammer might establish trust by impersonating a known connection or someone with authority, such as an IT professional or bank official. Under the guise of verifying the victim’s identity, they can then start to persuade them into sharing information that helps the fraudster carry out the attempted cyber-crime.
Phishing sometimes involves a blanket message sent to many users, while spear-fishing and whaling are highly targeted approaches aimed at a lower volume of recipients. Business email compromise (BEC) scams are a type of spear-fishing attack that uses email to deceive employees into facilitating a cyber-crime.
Other variations are phishing done by SMS (“smishing”) or voice phishing (“vishing”), which uses phone calls or deep fake technology to carry out pretexting.
Learn more about phishing in all its forms.
The short answer? Common enough to be concerning.
We know this from the Notifiable Data Breaches (NDB) Report, which the Office of the Australian Information Commissioner (OAIC) releases twice a year. The report delves into the volume and causes of data breaches that were reported to the Commission over the previous six-month period.
Under Australia’s NDB Scheme, any entity that’s covered by the Privacy Act has to notify the OAIC if it experiences a data breach in which:
These reports are a useful barometer for identifying trends in data breaches. And, when looking at reports from recent years, it’s clear that social engineering is steadily increasing as a cause of data breaches.
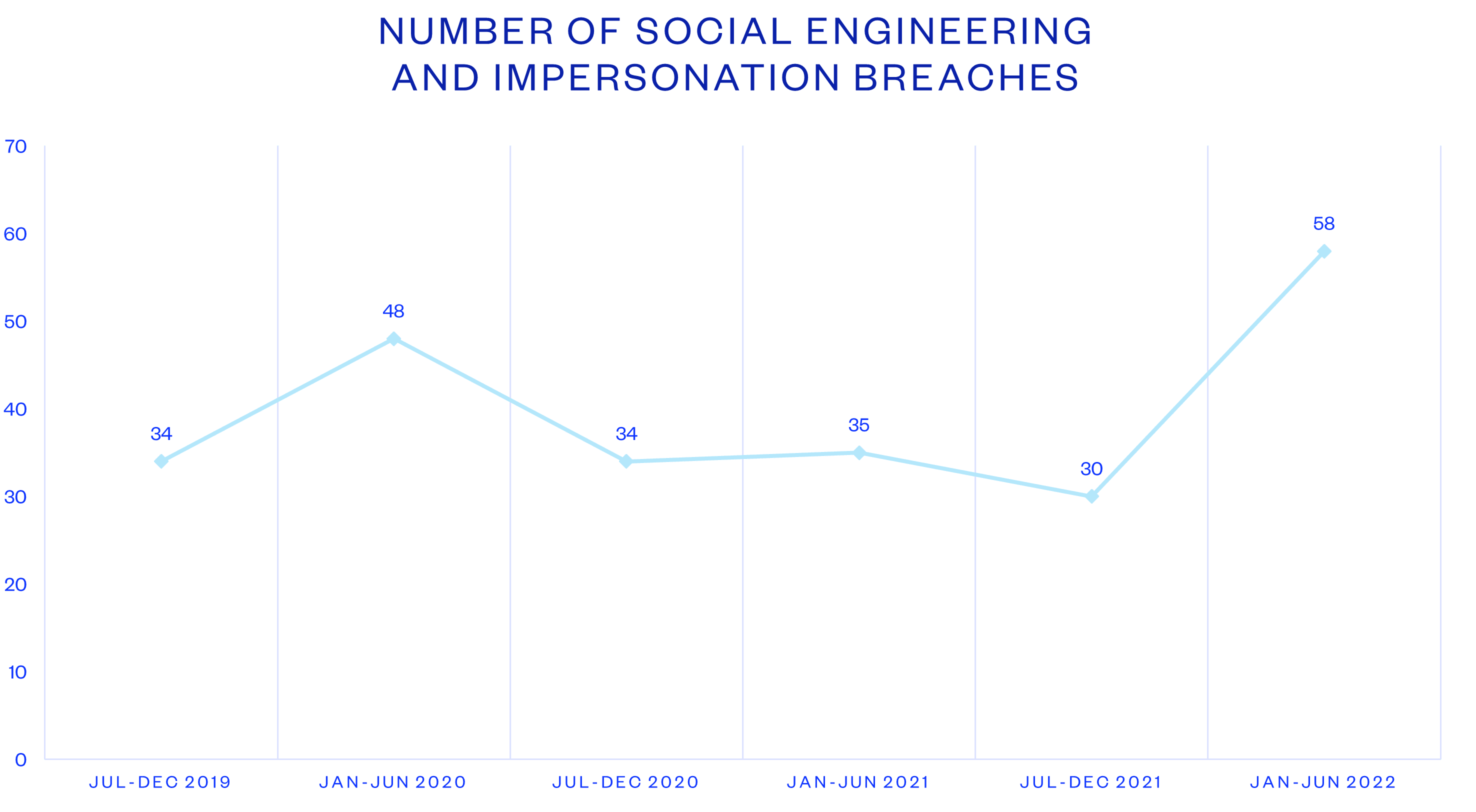
Source: OAIC
The latest NDB Report, covering January to June 2022, saw 58 reports of social engineering causing a data breach. That’s nearly double the 30 cases reported in the previous six-month period.
There’s no single solution that can protect against all forms of social engineering attacks, which is why finance leaders need to own their organisation’s cyber-crime strategy. This is the intersection between your financial controls and your cybersecurity strategy – without one, organisations tend to have gaps that cyber-criminals are learning to exploit with greater and greater frequency.
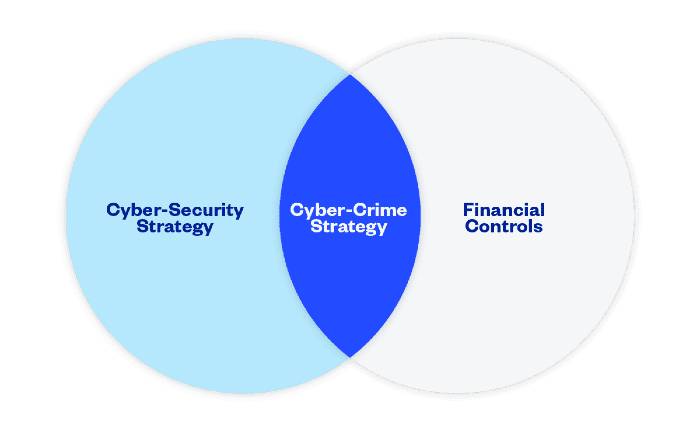
A cyber-crime strategy unites your cyberstrategy with your financial controls, pre-empting even some of the most cutting-edge cyber-crime tactics. But it includes a few different elements – some of those include better training and technology to arm your AP team against a fast-evolving generation of scammers and cyber-criminals.
Generally, AP staff aren’t trained to identify social engineering techniques. And, as we can see from our social engineering example, these deceptions are often very sophisticated and hard to identify. Despite this lack of training, AP staff tend to be primary targets of financially motivated cyber-criminals.
AP and finance professionals need dedicated cyber-crime training – beyond standard cybersecurity training, which usually only touches on basics and isn’t tailored to any particular organisational function. To effectively combat the growing diversity of cyber-crime tactics, leaders should consider finance-specific training, such as:
Of course, training is just one element of a healthy cyber-crime strategy. Others include fostering an anti-cyber-crime culture, ensuring you have the right tech stack and implementing the right processes and procedures.
Crowdstrike outage aftermath: Government warnings, scam attempts, and essential steps to safeguard your business from cybercriminals.
See how a Rite Aid data breach compromised 2.2M customers’ data through an elaborate impersonation attack. Learn about the risks and preventive measures.
AT&T’s data breach exposes phone records of 110 million customers in Snowflake cyber incident, highlighting cloud security risks. Learn more.
Eftsure provides continuous control monitoring to protect your eft payments. Our multi-factor verification approach protects your organisation from financial loss due to cybercrime, fraud and error.