A CFOs Guide to ACH Payments
In recent years, the banking industry has undergone significant transformations that have changed how we manage our finances. The shift from traditional …
As the financial industry continues to evolve, so do the regulations governing it. One of those regulations has generated significant attention in recent years – CPS 234, a directive from the Australian Prudential Regulation Authority (APRA) aimed at improving the resilience of the financial sector against cyber threats. Designed to help businesses better manage financial risk, CPS 234 can be a daunting prospect for those responsible for ensuring compliance.
But fear not – in this guide, we’ll take a closer look at CPS 234 and provide strategies for staying compliant to help ensure your business remains secure and resilient.
APRA CPS 234 is a regulation introduced by the Australian Prudential Regulation Authority (APRA) to improve the resilience of APRA-regulated entities against cybersecurity threats. This regulation was introduced in 2019 and applies to all APRA-regulated entities, including:
The primary objective of CPS 234 is to ensure that APRA-regulated entities maintain information security in a highly challenging and rapidly changing environment. It aims to do so by outlining clear cybersecurity requirements that APRA-regulated entities must adhere to.
CPS 234 requires APRA-regulated entities to maintain an information security capability commensurate with the size and complexity of their operations. It also requires them to notify APRA of any significant cybersecurity breaches, maintain information on their information security policies and practices, and demonstrate compliance with the regulation.
Why is this important for your businesses? Well, APRA-regulated entities that fall under the CPS 234 must comply with the regulation. Plus, by adhering to the regulation, organisations can maintain a strong cybersecurity posture to keep up with cyber-attacks that are increasing in frequency, sophistication and impact – which are all increasing even according to the under-reported numbers we’ve seen in the most recent Scamwatch report.
To comply with CPS 234, businesses must have a clear understanding of their information and financial assets, the threats and vulnerabilities according to those assets, as well as the potential consequences of a cybersecurity incident. They must also have appropriate information security controls in place, including policies and procedures for incident management, access management and vulnerability management.
CPS 234 also requires APRA-regulated entities to maintain a cybersecurity resilience posture and regularly test their information security controls to ensure their effectiveness. They must also have a system in place to review and assess the effectiveness of their cybersecurity practices regularly.
Businesses that fall under the scope of the APRA CPS 234 regulation must meet several key requirements and obligations to ensure compliance. We’ve outlined them below.
For more information on key requirements and what they mean, you can find the APRA CPS 234 information security whitepaper from the Institute of Internal Auditors Australia.
To comply with CPS 234, businesses must first identify the financial risks they face.
This includes risks associated with the threat landscape and broader risks such as market volatility, regulatory changes and operational risks. By conducting a thorough risk assessment, businesses can gain a better understanding of the potential financial risks they face and how they can mitigate them. For example, businesses may face the following financial risks:
To manage financial risks while remaining compliant with CPS 234, leaders need a comprehensive approach that addresses the various risks and requirements outlined in the regulation. This might involve implementing strategies around new policies and procedures, investing in new security technology or training staff to better manage cyber risks.
By taking a proactive approach to risk management, businesses can not only meet the requirements of the CPS 234 regulation but also improve their overall resilience and cybersecurity. Here are some ways to do that:
By implementing these strategies, organisations can effectively manage financial risks related to information security while remaining compliant with CPS 234. This can help ensure the long-term stability and success of the organisation.
The release of CPS 234 aims to minimise the likelihood and impact of information security incidents on the confidentially, integrity or availability of information assets.
Complying with this regulation can enhance your business’s cybersecurity stance by providing a structured framework for managing information security risks, staying up-to-date with emerging threats and best practices, and building trust with customers and stakeholders.
Organisations can take their cybersecurity strategy to the next level by incorporating strong, technology-enabled defences like Eftsure’s payment protection, helping to ensure long-term stability and cyber resilience.
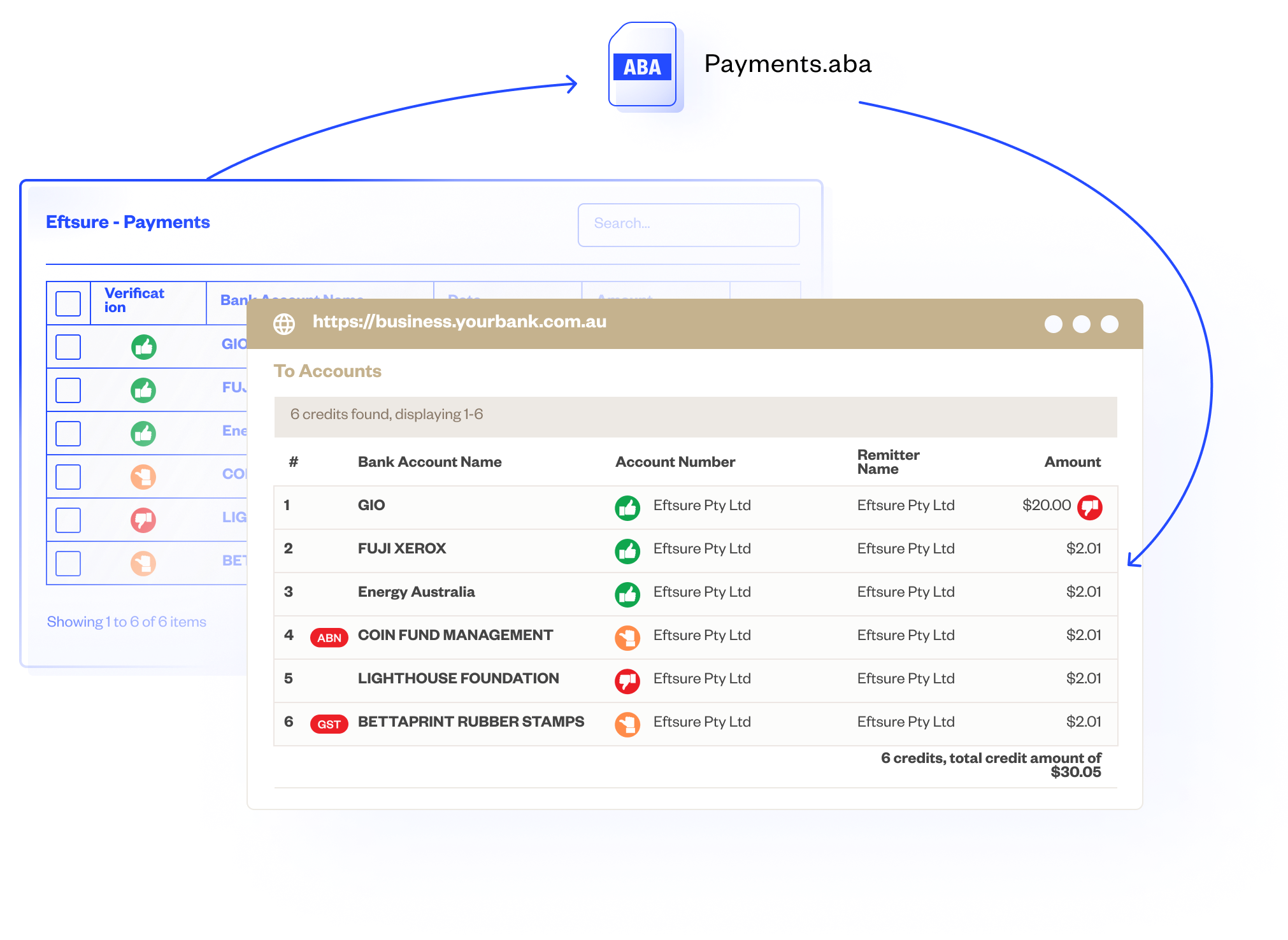
Our solution allows your organisation to align with the CPS 234 regulation by verifying Electronic Funds Transfer (EFT) when paying suppliers. Through our real-time thumb alerts, you can identify each outgoing payment and ensure it is being paid to the intended legitimate third party. This assures your AP team that they are not being defrauded when processing EFT payments, allowing you to manage financial risk.
Contact Eftsure today for a full demonstration of how we can mitigate financial risk.

In recent years, the banking industry has undergone significant transformations that have changed how we manage our finances. The shift from traditional …
Faster payments are part of our every day – but cybercriminals are exploiting the system. Discover how you can reduce the risks in your business.
Tired of yet another unwanted message in your inbox? Here’s how to reduce spam emails and text messages.
Eftsure provides continuous control monitoring to protect your eft payments. Our multi-factor verification approach protects your organisation from financial loss due to cybercrime, fraud and error.