Phishing is a common cyber scam whereby cybercriminals attempt to obtain personal information through fraudulent emails, text messages, or phone calls. Often, phishing attacks are effective because they pose as reputable companies, banking institutions, or government agencies to build trust while accessing highly sensitive information such as banking details, passwords, credit card numbers, and more.
The Inception of Phishing and How Common It Is Today
The term phishing was originally coined in 1996 when a group of hackers targeted users through the AOL (America Online) brand. At the time, AOL was a pioneer in the internet space and quickly became the most widely used and recognized internet provider in the United States.
During this period, AOL began to tighten security measures, but groups of hackers started impersonating the internet giant, sending falsified emails and messages to AOL customers disguised as the brand. Given this was a brand new era of digital communication, many consumers lacked awareness on the topic and quickly became victims of fraud and identity theft.
Since the mid-1990s, hackers and cybercriminals have only become smarter and better equipped in the space of phishing scams. It remains a huge and continuously growing problem today. According to Statista, phishing was the most prevalent scam in Australia in 2022, with over 74.5 thousand incidents reported.
Overview of the Types of Phishing Scams and Phishing Techniques
Email Phishing
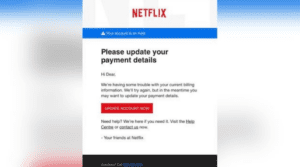
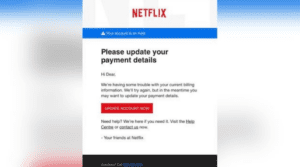
Hackers and cybercriminals will emulate a well-known organization, banking institutions, or government agencies via email to try and gain access to personal information and data. Sometimes the emails will contain links that, when clicked, take the user to a form to submit personal information or login details. In other instances, the emails may contain attachments that lead to the installation of malware if opened.
Spear Phishing
Similar to email phishing, spear phishing takes a similar approach but is unique in that it’s more tailored and targeted. Rather than sending emails to a large group of people at random, this would be an email attack focused on a specific group of people or organization. Spear phishing is a type of social engineering, and usually, emails will appear as if coming from a trusted person.
Smishing
Attacks over SMS messaging (text messages), usually containing malicious links. These can range from a falsified message from FedEx, encouraging you to update your details for an upcoming delivery, to messages containing information on claiming a prize.
Vishing (Voice Phishing)
These are criminal attacks made over the phone. Often a person will receive a phone call, and the caller will impersonate a bank or government agency, looking to gain access to personal information or incentivizing them to take action on something.
Business Email Compromise (BEC)
Cybercriminals gain access to business email accounts to impersonate people within an organization to get access to sensitive information or to prompt an action to take place, such as a funds transfer.
Pharming
This one is a bigger effort by hackers, where they will use redirects to guide users onto a malicious or fake website. These websites can appear almost identical to common e-commerce stores, allowing you to complete a purchase online while unknowingly giving personal, login, and credit card information.
Social Media Phishing
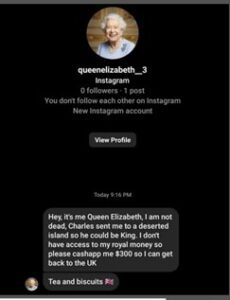
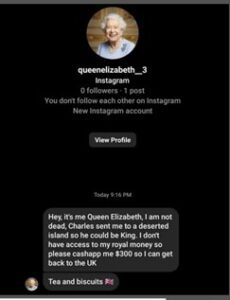
Cybercriminals will create fake accounts impersonating brands, government agencies, or even close friends, to reach out via direct message to start a conversation with the intent to gain sensitive information or money.
Clone Phishing
Hackers will replicate an existing email and either add or replace an existing link or attachment, which will result in adding malware to the recipient's computer. Other ways of using clone phishing can include the hackers adding a link to a cloned invoice, with updated banking details that, without proper payment protection in place, can go easily unnoticed by the recipient.
Search Engine Phishing
Similar to pharming, scammers will use search engine results to drive people to a malicious website on a false URL.
USB Phishing
Last but not least, never pick up an unknown USB. USB phishing leads to the downloading of malware onto a computer, which can then provide cybercriminals access to everything saved on the system.
Recognizing Phishing Attacks
Cyber scammers are always looking for their opportunity, targeting everyday people, organizations, and governments, so it’s important to remain vigilant. Unfortunately, we live in an era where it’s best to question everything, rather than assume any request for your personal information is 100% safe and secure.
Common Themes in Phishing Scams
According to the Federal Trade Commission, these are common themes in phishing emails:
You receive an email from a subscription service saying your payment failed, providing a link in the email to update your credit card details
A financial institution looking to confirm details about your personal banking information
You receive an invoice for something you don’t recognize, or for something you’ve already paid
An email from a government agency saying you are due for an unclaimed refund
How to Spot and Avoid Phishing Scams
Double Check the Email Address or Phone Number
In a phishing email, often scammers will change a single letter in an email address, or they will make a variation of a person’s or company’s email to make it seem legit.
Before Clicking Any Links, Check the URL
If the URL doesn’t appear to be to a legitimate website affiliated with the source of the request, don’t click it. For example, if you receive a text from AusPost to update your shipping details, but the link doesn’t mention Australia Post or the website, this could be a red flag for a malicious link.
Sometimes, if the URL is not evidently written in a message, it’s worth hovering over the button or link to see a preview of the link appear before you click anything suspicious.
Read All Messages with a Critical Eye
Many times, scammers and cybercriminals will use AI to help generate messages. Sometimes you’ll notice poor grammar or spelling mistakes in a message, which can signal it hasn’t come from a reputable or legitimate source.
If the Greeting Is Generic, It Probably Isn’t Legit
Banks and other reputable subscription software will have your personal details on file. If your messages are not personalized, but they are asking you for information, it’s best to contact the company directly and confirm if this is valid.
Double Check Social Media Accounts
When phishing messages are sent on social media, check the handle and details on the account to see how likely it's actually who they appear to be. If the account is new and/or lacks friends and followers or photos and details, don’t engage with the request.
When in Doubt, Reach Out
If you’re still unsure about a request for your information, it’s best to reach out to the company or person directly to confirm it’s them seeking the information. For example, if you receive a suspicious email from your bank, reach out to them over the appropriate channels (phone or email) and explain what you’ve received and ask if it’s safe to proceed with the request.
Note: if you’re looking for a phone or email, don’t take any information from the messaging source. Be sure to head directly to the company website from your browser and pick up actual contact details.
Proactive Measures to Protect Yourself from Scams
Keep Your Systems Up to Date
Ensure you’re constantly running updates on your electronic devices, especially when it comes to security upgrades to keep you safe from malware.
Always Use Multi-Factor Authentication (MFA)
This ensures when you log in to important accounts, you have a way to validate yourself as the user. MFA can include a text message code at login or using an authenticator code generator, such as Google Authenticator or Microsoft Authenticator.
Invest in Protection
From a personal perspective, this can look like installing anti-virus software on your laptop to keep hackers and scammers from getting into your personal devices. Alternatively, from a business standpoint, investing in tools like accounts payable protection software (Eftsure) provides an added layer of security to keep payments out of the hands of scammers. Falsified invoices or payment requests will be immediately flagged and checked, so funds always remain safe.
How to Report a Phishing Scam
Although we hope this part of our article never has to be used by our readers, it’s important anyone who feels they may have been affected by a scam receives the support they need as soon as possible.
What to Do If You’ve Been Scammed? How to Report a Scam
In the event you receive a phishing attempt, it’s important to report it, even if you were able to recognize it before submitting your details. The Australian Cyber Security Centre breaks down several different scenarios, with appropriate next steps to follow for phishing protection.
No matter what, be sure to report the scam to the National Anti-Scam Centre, and in the event you’ve become a victim, you’ll need to lodge a report through ReportCyber and then contact your financial institution.
Reporting helps to stop future scams, protect others in vulnerable situations, and ensures victims get the support they need to recover from potential hardship.
Summary:
Phishing is an extremely common cyber scam, whereby cybercriminals attempt to obtain personal information through fraudulent emails, text messages, or phone calls.
Phishing was the most prevalent scam in Australia in 2022, with over 74.5 thousand incidents reported.
There are 11 variations of phishing scams, all of which can be initiated through email, phone, social media, and search.
There are several key themes to help you spot a phishing email and/or other phishing attacks.
If you see a scam or believe you are a victim of a scam, report it to the National Anti-Scam Centre, lodge a report through ReportCyber, and contact your financial institution immediately.