What is vendor management?
Vendor management is the act of ensuring that your third-party vendors meet regulatory requirements and contractual obligations. This safeguards your business from …
Vishing (voice phishing) is when a caller makes a fraudulent attempt over the phone asking victims to release sensitive and personal information. Vishing, sometimes initiated with voice act is commonly used to gain access to information such as passwords, social security numbers, banking information and more.
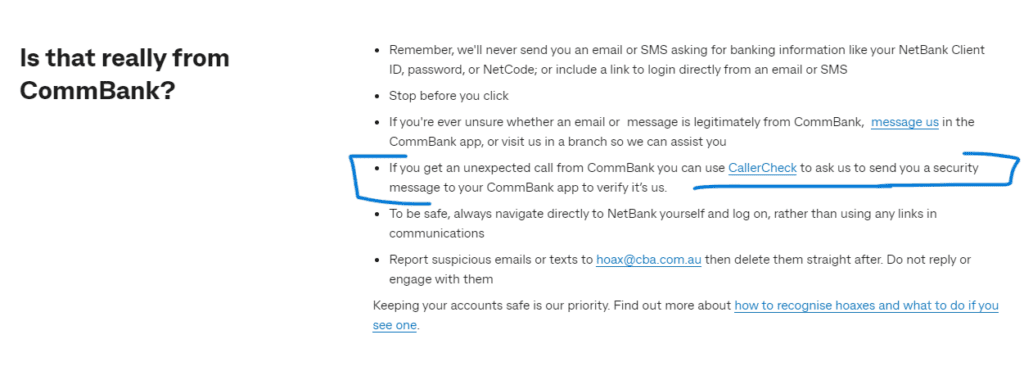
Cyber criminals and scammers may use their own voice or voice activated software and recordings to impersonate a trusted person, with the intent to gain access to personal data. For example, banks are often warning customers never to release their personal banking information over the phone, especially with an inbound call, without taking proper steps to verify it’s actually them.
Vishing is a type of social engineering focused on gaining a victims trust so they will divulge sensitive information. It may even result in the victim taking an action, such as sending funds on behalf of themselves or their company.
In the age of AI, ChatGPT and applications such as WormGPT, it’s becoming increasingly easy for cyber criminals to research and get access to a person’s contact information. Some scammers are even selling personal details on the dark web, making it easier than ever to find victims worth targeting. All this to say, scammers will do their research and then they will make contact – in the case of vishing, this contact will be made over the phone.
In more sophisticated attempts, scammers may couple their vishing attempts with other phishing tactics, such as a well-written phishing email before or after they make phone contact. In some instances, scammers may send an email on behalf of a trusted brand (ie. the bank or a company you may have a subscription with), notifying you of an issue with your account and asking you to contact them over the phone. Phone numbers may even be localised by area code, or they will be disguised under a 1-800 number, making it harder to decipher where the end person is located.
Once the scammers have accessed your personal information and had a moment to do a bit of research, they will tailor their vishing scheme to your unique situation or lifestyle. This can include, as mentioned above, impersonating your bank of choice, or in other more extreme situations, they may attempt to pressure victims by instilling a sense of urgency and fear, encouraging people to divulge personal information or transfer money immediately. In the age of deepfakes, vishing has escalated to a whole new level making it even harder to trust who is on the other side of the phone. Just this year, headlines broke telling people to ‘beware of virtual kidnapping ransom calls.‘
Cyber training experts warn of 7 common vishing scams today:
It’s important to stay current with cyber crime news, as the space is evolving quicker than ever. Because tactics are becoming more refined and harder to detect, the first line of defence is awareness and training. This should be a priority for individuals, as well as corporations and businesses.
Vendor management is the act of ensuring that your third-party vendors meet regulatory requirements and contractual obligations. This safeguards your business from …
Multi-factor authentication (MFA) is a security method that requires users to prove their identity using two or more distinct factors before accessing …
Imposter scams are a type of fraud where scammers pretend to be trusted individuals, companies, or government agencies to deceive victims into …
End-to-end B2B payment protection software to mitigate the risk of payment error, fraud and cyber-crime.