A CFOs Guide to ACH Payments
In recent years, the banking industry has undergone significant transformations that have changed how we manage our finances. The shift from traditional …
Finance leaders and their teams are often on the frontlines of cyber-crime, since the vast majority of cyber-crimes are financially motivated. Protecting your organisation’s money and reputation requires strong, up-to-date financial controls, but strong security practices – like the Essential Eight – help to prevent cyber-criminals from breaching or infiltrating systems and infrastructure in the first place.
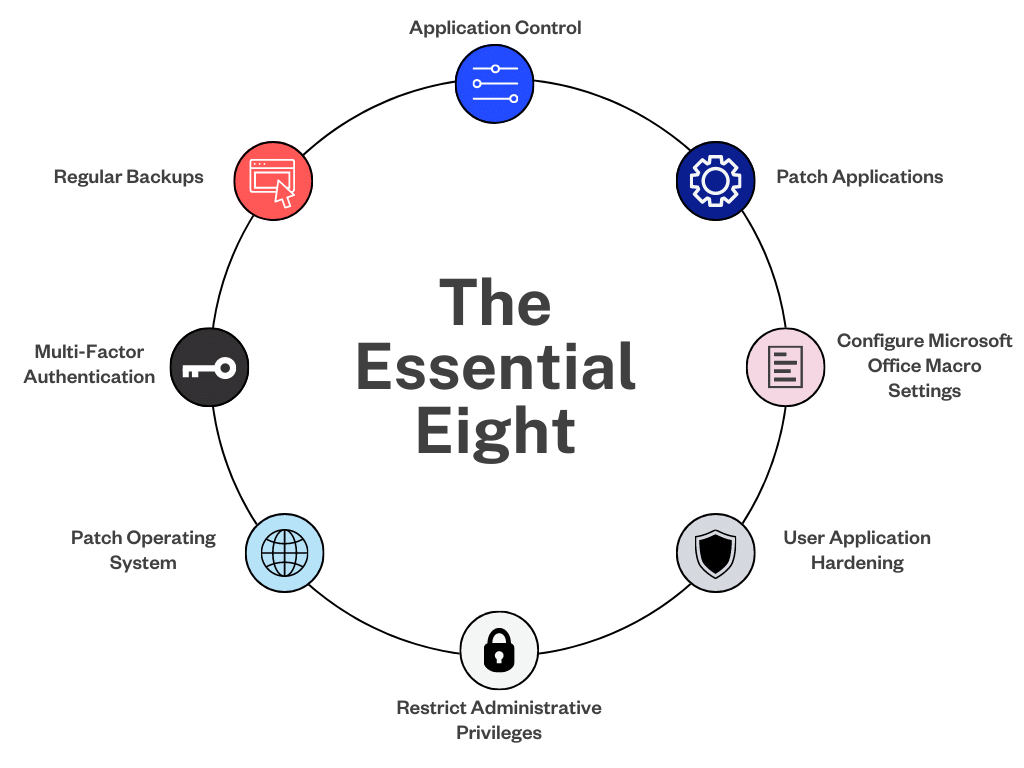
So what are the Essential Eight? They’re cybersecurity controls that make up a framework developed by the Australian Signals Directorate (ASD). When implemented correctly, they can significantly mitigate an organisation’s security risks.
In this article, we’ll explore the Essential Eight in detail, explain what financial professionals need to know about them, and outline how to work with your IT or security team to provide the best possible defence against cyber-criminals.
Originally starting as a set of only four controls, the ASD has fleshed out its initial security guidelines into the Essential Eight – these serve as a baseline for mitigating businesses’ cybersecurity incidents. No set of mitigation strategies can guarantee complete protection against all forms of cyber-crime, but the Essential Eight make it a lot more challenging for cyber-criminals to compromise network systems.
The ASD has also provided the Essential Eight Maturity Model, a framework that helps organisations assess their cybersecurity posture and maturity. This framework illustrates the effectiveness of these strategies and offers a means for organisations to measure their implementation of the Essential Eight.
The Essential Eight is an excellent starting point for businesses with limited resources to enhance their cybersecurity posture. These essential controls are designed to be easily implemented and cost-effective, making them accessible to organisations of all sizes and budgets.
By adopting this framework, businesses can substantially reduce their risk of falling prey to cyber attacks. For instance, patching vulnerable software minimises the likelihood of attackers gaining access through known exploits, while regular backups ensure critical data is not lost in the event of a successful breach attempt.
As a finance professional, it’s important to understand these strategies and work with your IT team to ensure your organisation is well-protected against cyber threats.
The ASD recommends using the Essential Eight as a foundation for securing Microsoft Windows-based, internet-connected networks. Designed to protect your IT systems and networks, the ASD provides different maturity levels for each control (meaning you don’t have to boil the ocean just to start implementing them, and you can continue enhancing the controls even after their initial implementation).
The controls’ main objectives are to prevent attacks, limit their impact, and secure data availability.
Once you have a grasp of these eight controls, your organisation can start assessing the best ways to tailor them to your business structure. So, what are the next steps?
To start checking your cybersecurity strategy against the Essential Eight, the ASD recommends conducting a four-stage assessment. This may require engaging with a security specialist experienced in conducting assessments for Essential Eight controls.
Those four stages are:
Conducting a thorough inventory of your IT systems and networks, evaluating the effectiveness of your current security measures, and identifying potential vulnerabilities in your system are all vital steps for assessing your current security posture. This can help identify areas that need improvement and allow you to prioritise implementation accordingly.
Here are some important steps to keep in mind when assessing your current security posture:
Begin by examining your current cybersecurity posture. At this stage, an assessor should try to identify the most suitable maturity level for your organisation.
Remember that even with limited resources, taking action and incorporating the Essential Eight can provide your business significant protection against cyber threats – and those cyber threats can cost your organisation in a variety of direct and indirect ways. Don’t save a bit of money today only to sacrifice more money (and even your organisational reputation) later on. And don’t hesitate to seek guidance from security experts if needed.
Consulting with an experienced cybersecurity specialist can help you get a clearer, objective understanding of your current posture and which changes to make. By assessing specific risk factors unique to your business, you can identify vulnerabilities and develop tailored strategies to mitigate cyber-crime, such as reviewing and testing the effectiveness of controls.
The right specialist can provide support beyond initial assessments and implementation, too. For instance, they can help identify more efficient technical solutions that address ongoing vulnerabilities and offer proactive support against ever-evolving cyber threats.
Partner with security experts who will:
Once assessments are complete you can start developing a security assessment report and map out the timeline to train employees. Cybersecurity training workshops and promoting an anti-fraud workplace are key components of an effective cybersecurity strategy.
First off, educating employees should be tailored and interactive. Invest in training workshops focused on educating employees about cyber risks, phishing attacks, password management and other best practices.
Additionally, you can minimise your risk of serious damage by encouraging staff members to promptly report any suspicious activity or potential breaches they notice. A strong security culture doesn’t mean that everyone has all the answers all the time – it means that employees aren’t afraid to put their hands up if an email looks dodgy, or to swiftly inform a manager if they think they clicked on the wrong link. And incorporating basic security protocols like MFA across all devices and accounts adds an extra layer of protection.
To effectively train your employees on security best practices, consider incorporating the following into your training program:
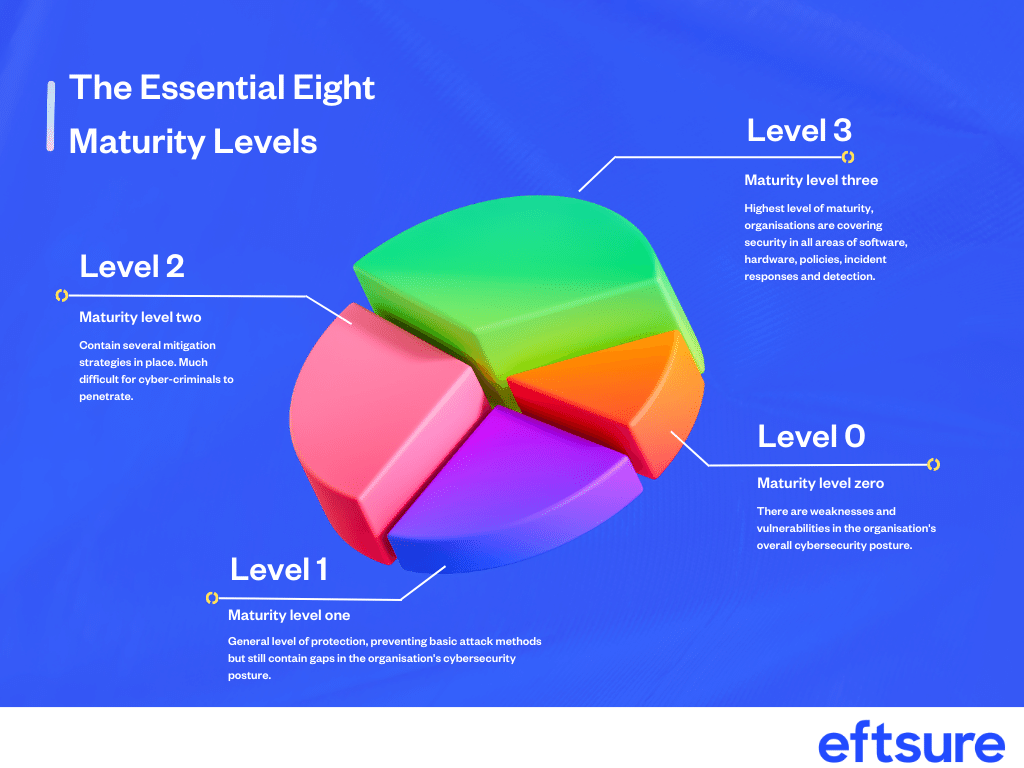
Once you have implemented the Essential Eight maturity model into your organisation, you can review the effectiveness of controls and begin working your way to increasingly mature versions of each control. Because the controls are designed to work together, organisations should aim to achieve similar levels of maturity across all eight controls.
The maturity model consists of four levels.
Requirements for each maturity level are outlined in Appendices A to C in this maturity model whitepaper.
The Essential Eight is endorsed by government agencies, making them a trusted blueprint for strengthening your cyber defences. And, if you’re a government agency, you might be required to implement them.
But it’s not just about whether the Essential Eight are mandatory – they have a few benefits that finance leaders should understand when working with security and IT teams.
For small businesses, implementing budget-friendly security measures is crucial.
The Essential Eight provides an affordable solution that can protect against a range of cyber threats. In fact, dealing with a cyber attack can end up costing more than implementing the Essential Eight in the first place.
Real-life examples exist of companies like MobileCorp that have saved money by using these eight strategies and preventing costly data breaches and system intrusions. By choosing to implement the Essential Eight, businesses can achieve cost-effective protection against common attack methods without breaking their IT budgets.
The Essential Eight is a comprehensive framework that helps businesses protect their IT systems and networks against some of the most common attack methods. We know from cyber-crime statistics that attack methods include popular tactics like phishing, BEC attacks, ransomware and malware. Each method can cause significant harm to a business’s IT system, resulting in data breaches, financial losses or operational disruptions.
The strategies are recommended by the ASD to provide a more cost-effective method to respond to a large-scale cyber security incident. By implementing these strategies such as application whitelisting and patching applications promptly, businesses can significantly reduce their risk of falling victim to cyber-attacks.
Cybersecurity statistics demonstrate that cyber-crime is an ever-growing threat to all businesses, no matter the size. As we’ve seen in the past with high-profile attacks like Optus and Latitude Financial, businesses of all sizes can fall victim to serious cyber incidents, making it important for every organisation to strengthen their cybersecurity strategies.
Using the Essential Eight as the foundation for your cybersecurity posture can help protect against data breaches and security threats. However, sophisticated cyber-criminals continue to adapt and are always hunting for ways to leverage new technology against legitimate organisations.
To keep up with this threat, your cybersecurity strategy will also need to evolve.
That’s why it’s crucial that you combine your cybersecurity strategy and financial controls to create an effective cyber-crime strategy. A cyber-crime strategy allows you to align elements together like segregation of duties and email security, adding later-stage protections that protect your organisation even if cyber-criminals manage to infiltrate your systems (or those of a supplier). This helps you protect your organisation from some of the most serious consequences of cyber-crime and fraud attempts.
In recent years, the banking industry has undergone significant transformations that have changed how we manage our finances. The shift from traditional …
Faster payments are part of our every day – but cybercriminals are exploiting the system. Discover how you can reduce the risks in your business.
Tired of yet another unwanted message in your inbox? Here’s how to reduce spam emails and text messages.
Eftsure provides continuous control monitoring to protect your eft payments. Our multi-factor verification approach protects your organisation from financial loss due to cybercrime, fraud and error.